For decades, ID badges have been a simple and effective way to control access to and within buildings.
An employee taps a badge.
A door unlocks.
The system logs the event.
Because the process works so seamlessly, many organizations rarely think about the technology behind the credential.
The reality, however, is that a large percentage of access credentials still in use today were designed more than thirty years ago. While cybersecurity defenses have evolved rapidly, many physical access control systems continue to rely on credential technologies that offer little protection against cloning or unauthorized duplication.
At the same time, buildings themselves are becoming smarter. Access control systems are increasingly integrated with identity management platforms, surveillance systems, and operational technologies across the organization.
As this ecosystem grows, the risks associated with legacy badge technologies are becoming increasingly difficult to ignore.
The Security Problem with 125 kHz Proximity Cards
Low-frequency 125 kHz proximity cards, commonly known as Prox cards, remain one of the most widely deployed access credentials in North America.
They gained popularity because they were simple, reliable, and inexpensive to deploy. For many years, they served organizations well as a convenient replacement for mechanical keys.
However, they were never designed to defend against modern security threats.
Proximity cards operate by transmitting a fixed identification number to a reader. If the information matches a credential stored in the access control database, the system grants access.
The identifier itself is not encrypted.
If someone captures that number, it can be copied.
Devices capable of reading and duplicating Prox credentials are inexpensive and widely available. Security researchers and physical security professionals have repeatedly demonstrated how easily these cards can be cloned using handheld RFID tools.
From the perspective of the access control system, the copied credential is indistinguishable from the original card.
That means a cloned badge can unlock doors, trigger access events, work in additional systems utilizing the cards, and appear in security logs under the identity of the legitimate employee who owns the badge.
A Real-World Example of Credential Cloning
Security analysts have repeatedly demonstrated the weaknesses of legacy proximity cards.
In one widely referenced physical security test, researchers used a low-cost RFID cloning device to copy several proximity credentials used in real facilities.
The cloned cards worked immediately.
Doors unlocked.
Access events were logged normally.
The systems treated the duplicated cards as legitimate credentials.
From the system’s perspective, nothing unusual occurred.
In reality, however, two identical credentials now existed, and the organization had no reliable way to determine which one was used.
This is one of the most significant concerns with legacy credential technologies. Once cloning occurs, accountability is lost.
Why Modern Security Ecosystems Raise the Stakes
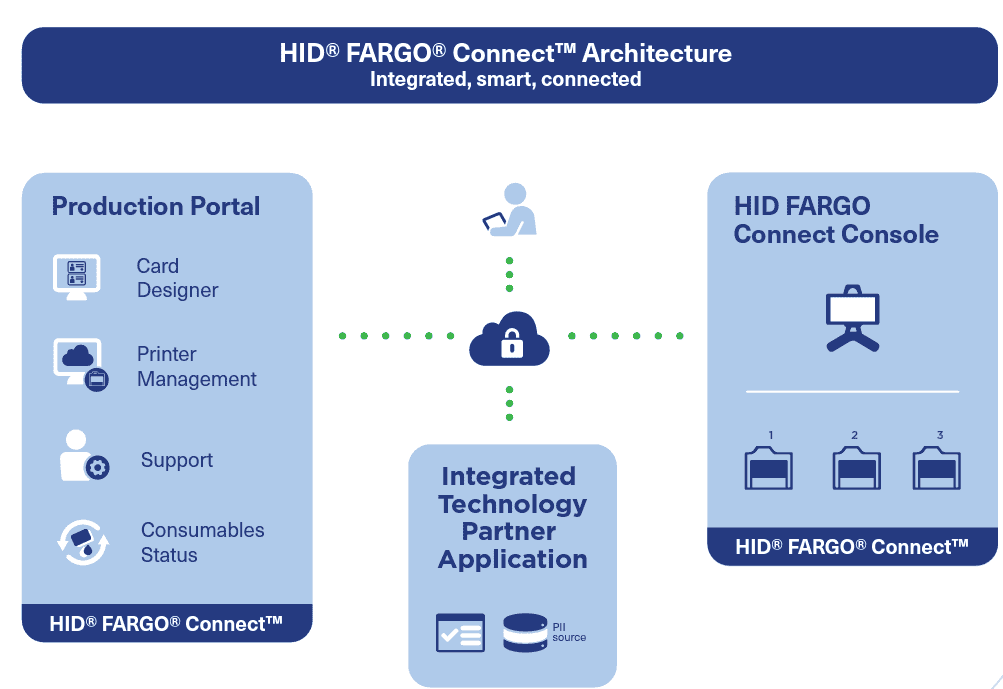
The risks associated with weak credentials become even greater as organizations move toward interoperable security systems.
What are interoperable security systems? Interoperable security systems are security technologies designed to work together seamlessly, even if they come from different manufacturers or platforms.
Instead of operating in isolation, these systems share data, communicate in real time, and coordinate responses.
Access control platforms today rarely operate as standalone systems. Instead, they are integrated with a wide range of technologies across the organization, including:
- Video surveillance platforms
- Visitor management systems
- Human resources and identity governance platforms
- Building automation systems
- Incident management tools
These integrations allow organizations to automate provisioning, manage identities more efficiently, and improve operational visibility across facilities.
But they also mean that a compromised credential can impact multiple systems simultaneously.
A cloned badge may not simply unlock a door. It could also generate inaccurate identity records, trigger automated building events, or grant unauthorized access to multiple restricted areas.
As organizations build more connected security environments, the strength of the credential itself becomes more critical.
ID Cards Are Now Used for Much More Than Doors
Credential technologies such as HID SEOS provide strong encryptionand allow a single badge to securely support multiple services throughout an organization. Prox technology can also support multiple functions, but if compromised, the cards will work across all associated systems, making encryption critical in today’s security and IT ecosystems.
In many environments today, ID cards support functions such as:
- Time and Attendance Management
- Healthcare Identification and Medical Workflows
- Cashless Payments
- Visitor Management
- Logical Access
- Smart Printing
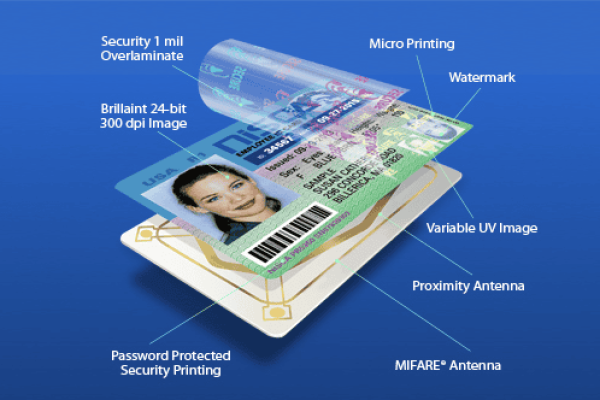
Many organizations are also deploying multi-technology credentials that combine several chip technologies on a single badge. This enables organizations to support multiple systems at the same time while gradually transitioning to newer technologies. These cards also make it easier to move from legacy access control readers to models that support more secure technologies. Large organizations often need to replace thousands of readers, and the new generation of access control readers, such as HID Signo, can support both legacy technology (Prox) and newer, more secure technology (HID SEOS) simultaneously during the transition.
For example, a single card may support secure building access, secure printing, and payment systems, while still maintaining compatibility with older infrastructure during transition periods.
Organizations exploring these strategies can learn more about this approach in this article: The Power of Combining Technologies on ID Cards for Enhanced Functionality
When a credential becomes the key to multiple operational systems, protecting that credential becomes significantly more important.
A cloned badge no longer represents only a door access problem. It can affect time and attendance, operational systems, and identity records across the organization.
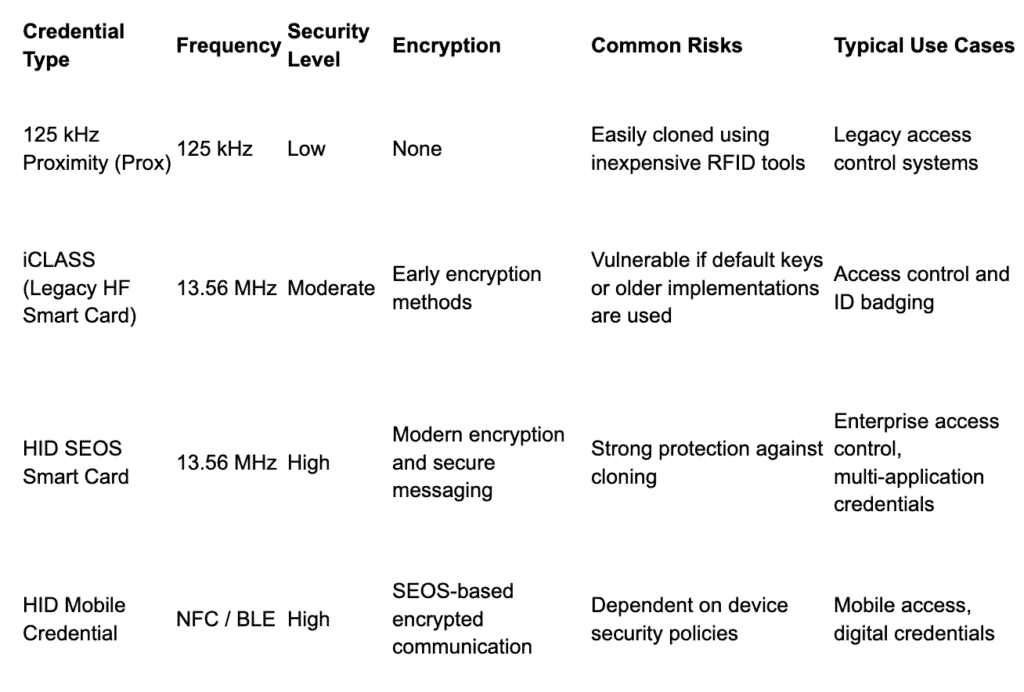
Credential Technology Comparison
As organizations evaluate upgrades, it helps to understand the differences between common credential technologies.
Stay tuned for part two, where we discuss why organizations are migrating to secure smart credentials and how that helps their future strategy. Then, part three will discuss mobile credentials.
Not sure where to start? If you would like to discuss your organization’s ID program, security goals, or upcoming projects, we would be happy to help. Call (800) 860-9111, contact your ID consultant, or Contact Us to schedule a consultation and explore the options available for your environment.
ABOUT THE AUTHOR: Since starting in 2015, Bill Eglet has become a seasoned professional who has served as Vice President of Sales and Marketing in the Identification industry. With extensive experience, Bill has unmatched expertise in ID badging, visitor management, and broader identification solutions. His insights offer valuable perspectives for navigating the complex world of identification technologies and industry trends, helping you stay ahead in this constantly evolving field.